Protection matrix
From Erights
(Difference between revisions)
(→Definition) |
|||
| Line 5: | Line 5: | ||
* columns correspond to particular objects | * columns correspond to particular objects | ||
and the context of each cell determines what operations on a particular object are permitted for a particular subject. | and the context of each cell determines what operations on a particular object are permitted for a particular subject. | ||
| + | |||
| + | == Example == | ||
| + | |||
| + | If: | ||
| + | * we have only three different subjects (1, 2 and 3) | ||
| + | * eight different objects (six files and a printer and a plotter) | ||
| + | * we recognize three different operations with objects (read, write and execute) | ||
| + | then one possible protection matrix may be: | ||
| + | |||
| + | [[Image:Protection matrix1.png]] | ||
Revision as of 12:41, 16 June 2009
Definition
One way how to capture the permissions of subjects to perform various operations with objects is to use a large matrix where:
- rows correspond to particular subjects
- columns correspond to particular objects
and the context of each cell determines what operations on a particular object are permitted for a particular subject.
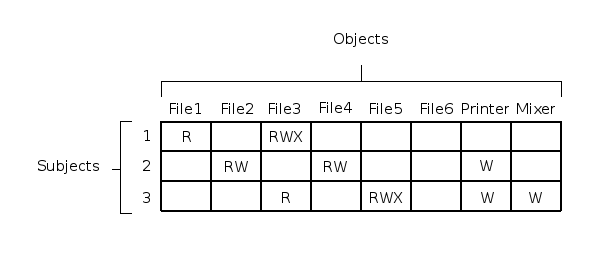
Example
If:
- we have only three different subjects (1, 2 and 3)
- eight different objects (six files and a printer and a plotter)
- we recognize three different operations with objects (read, write and execute)
then one possible protection matrix may be: