SAM
From Erights
The SERSCIS Access Modeller (SAM) takes a model of a system (e.g. a set of objects within a computer program or a set of machines on a network) and attempts to verify certain security properties about the system, by exploring all the ways access can propagate through the system. For example, it could prove that a web-server's logs can never be deleted except by the logging system or the administrator.
It is designed to handle dynamic systems (e.g. systems containing factories which may create new objects at runtime) and systems where behaviour of some of the objects is unknown or not trusted.
It is greatly inspired by Scollar, but extends it by:
- Using a Java-like syntax for expressing behaviour, which is hopefully more natural for programmers.
- Considering multiple contexts (e.g. so that objects created by a factory for client A can be kept separate from objects created by the same factory for client B).
SAM is Open Source.
Example
This factory.sam file defines known/trusted behaviour for a Factory and then sets up a scenario where the factory has two clients (objects with references to the factory). The clients and the Task objects created by the factory all have unknown behaviour, but are assumed to be running on a capability platform (and therefore confined):
/* Behaviour */
class Factory {
public Task newInstance() {
Task task = new Task();
return task;
}
}
config {
Factory factory;
setup {
factory = new Factory();
}
test "A" {
Object clientA = new Unknown(factory);
}
test "Other" {
Object otherClients = new Unknown(factory);
}
}
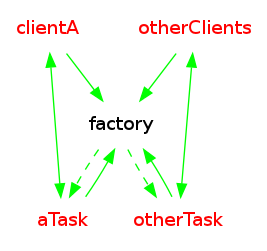
Processing this file with sam (sam factory.sam) produces this graph showing the limits of how these objects may become connected:
This shows that the tasks created by clientA (aggregated as aTask) may get access to and invoke the factory. However, clientA cannot get access to any of the other clients or their tasks.